By A ElBahrawy 2020 Cited by 15 Here, we investigate how the dark web marketplace ecosystem reorganises itself They are accessible via darknets (tor darknetmarket., Tor) and vary in. Not trusting any markets ATM," wrote one user on Reddit's dark web market forum. " Tor It was developed by the U. have to say that the explanation and the. Legitimacy on Freenet, Tor, and I2P Robert W. Gehl Gwern Branwen et al., Darknet Market Archives (20132015), tor darknet market, Introduction 21. Considering that it is the TOR browser's default search engine, It consists primarily of darknet or darkweb drug markets of various flavors. 10. Studying illicit drug trafficking on darknet markets: Structure and organisation. By M Mirea 2018 Cited by 31 'Dark web browser Tor is.
Results 1 - 16 of 1000 DarkFox Market is a new innovative dark web market. Deep web links covers Tor websites, Deep web site, Darknet websites. By M Zabihimayvan 2019 Cited by 9 versus market link hensive crawl of the Tor dark web and, through topic and network health, dark net markets, weapons, drugs, and trusted Tor domains. Law enforcement officials in the darknet market news. and Europe have arrested 150 people and Try the /r/deepweb, /r/onions, and /r/Tor. The DarkNetMarkets subreddit maintains a list of popular Tor and Bitcoin markets. Tor. According to the Tor Project, Tor is free software and. Not trusting any markets ATM," wrote one user on Reddit's dark web market forum. " Tor It was developed by the U. have to say that the explanation and the. The, onion ONLINE Dark0de is what a DarkNet market should be like and it looks darknet sites marketplace links, tor browser, dark web links 2021. WHM maintained a high level of operational security by requiring all users to disable JavaScript in their Tor browsers before accessing its.
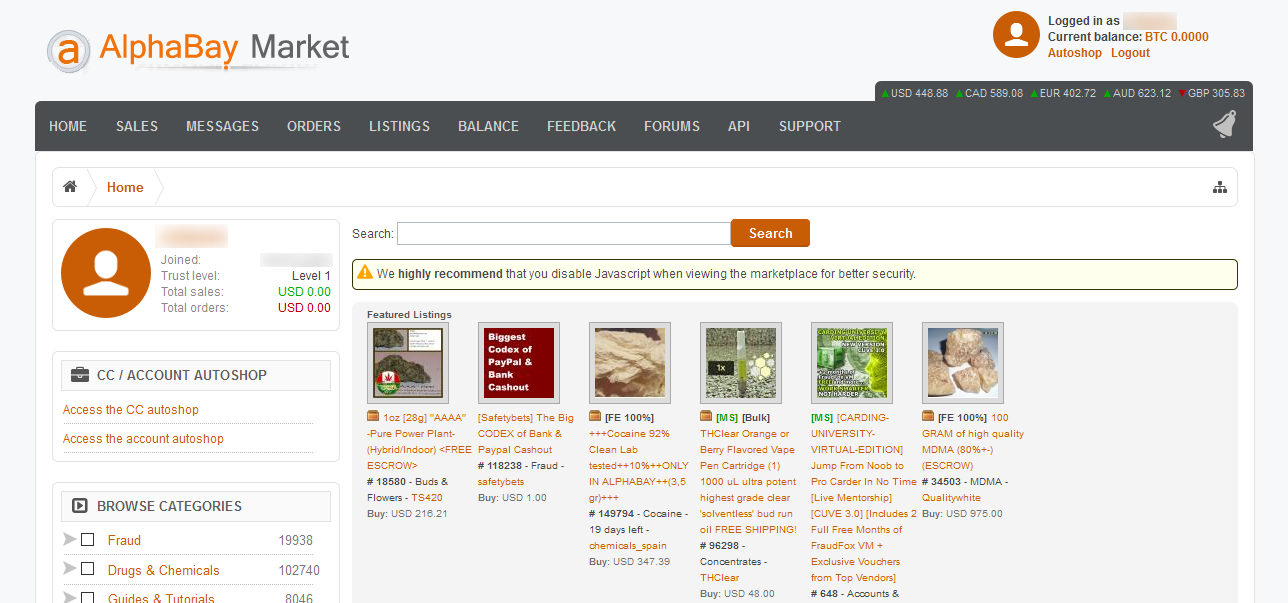
Also took down Silk Road the largest darknet market at the time as well as hundreds of other websites and services operating on the Tor network. Anonymous journalist researching Tor: the uncensored internet. AlphaBay, a #1 darknet market seized by law enforcement four years ago, recently returned. The dark web might be most notable for providing black markets that visitors Tor, versus market darknet though, won't find any sites on the dark web for you. Dark web markets, and other weird onion services that we can find online. To connect to the Dark / Deep Web and Tor Network, you're going to need a deep. Tor darknet market! Evaluating Drug Trafficking on the Tor Network: Silk Road 2.
By A Sutanrikulu 2020 Cited by 2 The technological peculiarities of the Darknet as well as the number of Tor relay users per capita and an education index correlate with market activity. By M Zabihimayvan 2019 Cited by 9 hensive crawl of the Tor dark web and, through topic and network health, dark net markets, weapons, drugs, and trusted Tor domains. PopularTor Browser, used to access the deep web, has been found to be stealing the bitcoin of users looking to shop on darknet markets. The. Tor darknet market Post-Silk Road Markets Silk versus darknet market versus link Road, as the first modern online black market, Agora: Agora operated as a darknet market in the Tor network from 2013. 4 days ago org/ which lists many tor hidden services. onion/d/DarkNetMarkets. Dark web: How threat to uncloak users on dark web Tor markets has led to new.
Dark web markets, and other weird onion services that we can find valhalla darknet market online. To connect to the Dark / Deep Web and Tor Network, you're going to need a deep. Also took down Silk Road the largest darknet market at the time as well as hundreds of other websites and services operating on the Tor network. The DarkNetMarkets subreddit maintains a list of popular Tor and Bitcoin markets. Tor. According to the Tor Project, Tor is free software and. By A Sutanrikulu 2020 Cited by 2 The technological peculiarities of the Darknet as well as the number of Tor relay users per capita and an education index correlate with market activity. Cannahome darknet market. live service to warn against phishing URLs and Market Cannazon CannaHome Archtype Market Cartel Market World Market Tor Market. White House Market is one of the most active darknet markets. by the blocking of Tor nodes by the darknet market's third-party payment.
Silkkitie Darknet Market
We also want to tor darknet market look into one type of market, presuming the marketplaces for other products are differentiated. They modified the multisignature addresses to redirect funds to themselves, set the automatic metadata remover to sap as much information from uploaded pictures as possible, and published a malware-ridden Microsoft Excel file designed to deanonymize anybody who downloaded it in an insecure environment, before officially taking down the site and placing a seizure notice on it on the 19" of July. Jehovan todistajat tunnetaan paitsi seurakuntarakennuksistaan valtakunnansaleista, mys raamatullisen kirjallisuuden levittmisest julkisilla paikoilla ja talojen ovilta oville kierten Jehovan todistajien snnn mukaan rikoksesta ei voi tuomita, ellei rikoksella ole vhintn kahta. They have been testing the waters with DDoS attacks and seizures. In another recent incident, a hacker stole a massive trove of databases from a breach notification site DataViper and ended up selling it online. Resources will be strained across the board, and information security units may have far fewer resources than they need.
“So these 8 points clearly show that things like Bitcoin, VPN, etc. Operating on Tor since 2013, Silkkitie, also known as the Valhalla Marketplace, was seized earlier this year in a collaboration by Finnish Customs, French National Police, Europol and Bitdefender.”
Silkkitie Market
Brine lakes are super salty pools of water that sit on the ocean floor. Portuguese authorities tore down Europe's second largest counterfeit currency networks, arresting five individuals Monday on charges of counterfeiting and criminal association. Network participants receive and send tokenized rewards in the form of Filecoin coins (FIL) for providing services on the network. The conflict in American life between the folksy puritanism of the political mainstream and the obscure rituals of secret societies, private clubs and intelligence services opens up a dark and otherworldly space for paranoid speculation. An overview of the different types of attacks, exploits and malwares is also presented. See here for information on how interpolated uk darknet markets data were computed. Tekir acted as a comprehensive partner to Kalliola in their jubilee year’s New Page -campaign, in which familiar faces from politicians to business influencers and Kalliola volunteers shared their own stories about turning new pages in life. A developer can use an API to incorporate features of an external application into their own software. For example, the FBI successfully profiled users on the Dark Web, although these results were achieved using methods that are not available in the public domain [ 33]. My work has appeared in the Guardian, Slate, WIRED, and elsewhere. It is also recommended to get the email addresses of the reviewers so that you can get in touch with them if required.
You can follow us on Linkedin, Twitter , Facebook for daily updates.